How to Add Security Headers to WordPress with WP Ghost
June 17, 2024
This tutorial has moved to the new WP Ghost Knowledge Base where each feature is presented in detail.
Add seven security headers to your WordPress site with one toggle in WP Ghost. Security headers protect against cross-site scripting, clickjacking, MIME type sniffing, and protocol downgrade attacks at the browser level.
What Are Security Headers
Security headers are directives included in the HTTP response from your web server. They tell the browser what it is allowed to do with your page content: which domains can load scripts, whether the page can be embedded in an iframe, whether to enforce HTTPS, and how to handle MIME types. Each header addresses a specific attack vector.
Without security headers, browsers apply default permissive policies. Attackers exploit these defaults to inject scripts, embed your pages in malicious iframes, or trick browsers into executing files with incorrect MIME types. Security headers close these gaps by setting explicit policies at the browser level.
WP Ghost adds all seven security headers with a single toggle, covering the protections that security auditors and tools like SecurityHeaders.com check for.
Why Security Headers Matter for Hack Prevention
WP Ghost’s 8G Firewall blocks malicious requests at the server level. Security headers protect at the browser level. They prevent attacks that happen after the page has loaded, like injected scripts executing in a visitor’s browser or your page being embedded in a phishing site. Together, they cover both sides of the connection.
Security auditors and scanners check for them. Tools like SecurityHeaders.com, Qualys SSL Labs, and Google Lighthouse grade your site based on header presence. Missing headers lower your security score, which can affect client trust and compliance requirements.
They require zero maintenance once enabled. Unlike firewall rules that get updated with new attack patterns, security headers are set-and-forget directives. Once active, they apply to every response with no ongoing configuration and no performance impact.
How to Enable Security Headers in WP Ghost
1. Go to WP Ghost > Firewall > Header Security.
2. Switch on Add Security Headers for XSS and Code Injection Attacks.
3. Click Save.
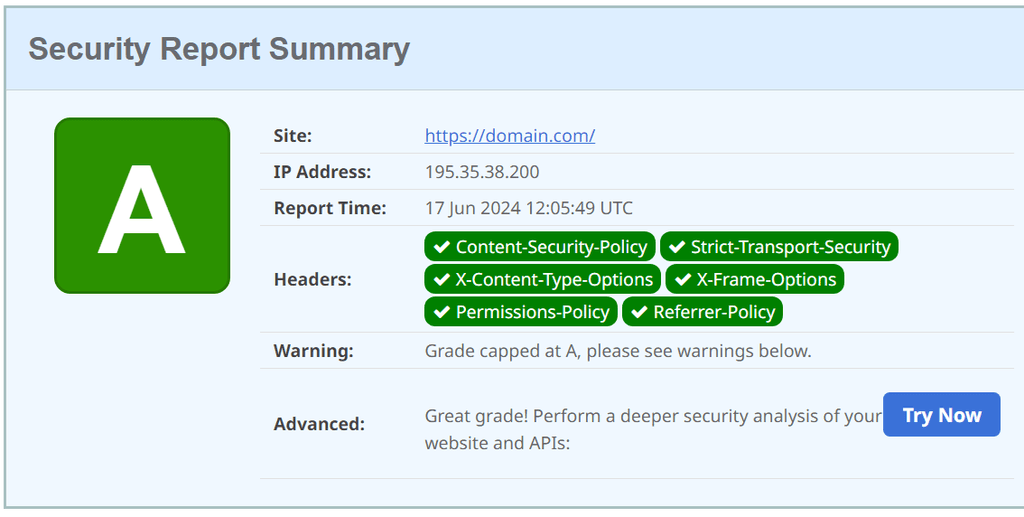
WP Ghost adds all seven headers through the server configuration file and PHP output. After enabling, verify your headers at SecurityHeaders.com by entering your domain. You should see green marks for all configured headers.
Security Headers Reference
Strict-Transport-Security (HSTS)
Forces browsers to access your site only over HTTPS, preventing protocol downgrade attacks and cookie hijacking. Once a browser receives this header, it will not make HTTP requests to your domain for the specified duration.
Strict-Transport-Security: max-age=31536000; includeSubDomains; preloadmax-age=31536000 sets the duration to 1 year in seconds. includeSubDomains applies the rule to all subdomains. preload requests inclusion in browsers’ built-in HSTS list for immediate enforcement even on the first visit.
Content-Security-Policy (CSP)
Controls which sources can load content on your pages, including scripts, stylesheets, images, fonts, and frames. Prevents XSS by blocking unauthorized script execution. This is the most powerful and most complex security header.
Content-Security-Policy: default-src 'self'; script-src 'self' https://apis.google.comdefault-src ‘self’ allows resources only from your own domain. script-src ‘self’ https://apis.google.com allows scripts from your domain and Google APIs. Customize the CSP based on which external services your site uses (analytics, fonts, payment gateways, live chat, etc.).
CSP requires careful configuration. A restrictive CSP can block legitimate third-party scripts like Google Analytics, payment gateways, or chat widgets. Test thoroughly after enabling. If a feature breaks, add the required domain to the appropriate CSP directive. WP Ghost lets you customize the CSP value directly.
X-Frame-Options
Prevents clickjacking attacks by controlling whether your page can be embedded in an iframe, frame, embed, or object element on other sites.
X-Frame-Options: SAMEORIGINDENY prevents all framing entirely. SAMEORIGIN allows framing only by your own domain. Use SAMEORIGIN if your site uses iframes internally, as some page builders and admin panels require this to function.
X-XSS-Protection
Enables the browser’s built-in XSS filter, which detects and blocks reflected cross-site scripting attacks. While modern browsers rely more on CSP, this header provides backward-compatible protection for older browsers.
X-XSS-Protection: 1; mode=block1 enables the XSS filter. mode=block instructs the browser to block the page entirely if an XSS attack is detected, rather than attempting to sanitize it.
X-Content-Type-Options
Prevents MIME type sniffing, where browsers try to guess a file’s type regardless of the declared Content-Type. Without this header, an attacker could upload a malicious file disguised with an innocent extension and the browser might execute it.
X-Content-Type-Options: nosniffnosniff forces the browser to use the declared MIME type. No guessing, no interpretation, no execution of mistyped files.
Cross-Origin-Embedder-Policy (COEP)
Ensures your document can only load cross-origin resources that explicitly grant permission. Prevents data leaks through embedded content from other domains.
Cross-Origin-Embedder-Policy: require-corprequire-corp requires cross-origin resources to include a Cross-Origin-Resource-Policy header granting access. Resources without this header are blocked.
Cross-Origin-Opener-Policy (COOP)
Isolates your document from cross-origin windows, preventing attacks like cross-origin information leaks and Spectre-type side-channel attacks.
Cross-Origin-Opener-Policy: same-originsame-origin isolates the browsing context so cross-origin documents can not interact with your page through window.opener or similar mechanisms.
Troubleshooting
A third-party service stopped working after enabling headers. This is almost always caused by Content-Security-Policy blocking scripts from external domains. If Google Analytics, a payment gateway, live chat widget, or embedded video stops working, add the required domain to the appropriate CSP directive. WP Ghost lets you customize the CSP value directly in the Header Security settings.
Page builder preview or iframes not loading. If your page builder’s preview or an iframe embed stops working, the X-Frame-Options header is likely set to DENY. Change it to SAMEORIGIN to allow framing by your own domain while still blocking cross-origin framing.
SecurityHeaders.com still shows missing headers. Clear your server cache and CDN cache after enabling the headers. Some caching layers serve old cached responses that do not include the new headers. Also check if your hosting provider sets conflicting headers at the server level, which can override the ones WP Ghost adds.
Frequently Asked Questions
Which headers should I enable?
All of them. WP Ghost enables all seven with a single toggle. The headers are industry-standard security practices recommended by OWASP and checked by SecurityHeaders.com. The only one that typically needs customization is Content-Security-Policy, which may need additional domains added if you use third-party services.
How do I verify my headers are working?
Visit SecurityHeaders.com and enter your domain. It scans your HTTP response headers and grades each one. You can also check headers in your browser DevTools under the Network tab: select a request and look at the Headers section.
Do security headers affect performance?
No. Security headers are a few bytes added to each HTTP response with zero impact on page load time, rendering speed, or server performance.
Do security headers affect SEO?
Not directly, but HSTS contributes to HTTPS enforcement which is a Google ranking signal. Google Lighthouse also checks for security headers in its security audit. Having proper headers can contribute to a better Lighthouse score.
Are security headers included in the free version of WP Ghost?
Yes. All seven security headers are fully included in WP Ghost free. There are no limitations on header functionality in the free version.
Does WP Ghost modify WordPress core files?
No. Security headers are added through server configuration and PHP output. No core files are modified. Disabling the feature removes all headers instantly.


