Add seven security headers to WordPress with one click in WP Ghost. Protect against XSS, clickjacking, MIME sniffing, and protocol downgrades with HSTS, CSP, X-Frame-Options, and more.
Security Feature
Block access to your entire WordPress site or specific paths like login and checkout from selected countries. WP Ghost Premium uses IP geolocation to restrict traffic from high-risk regions.
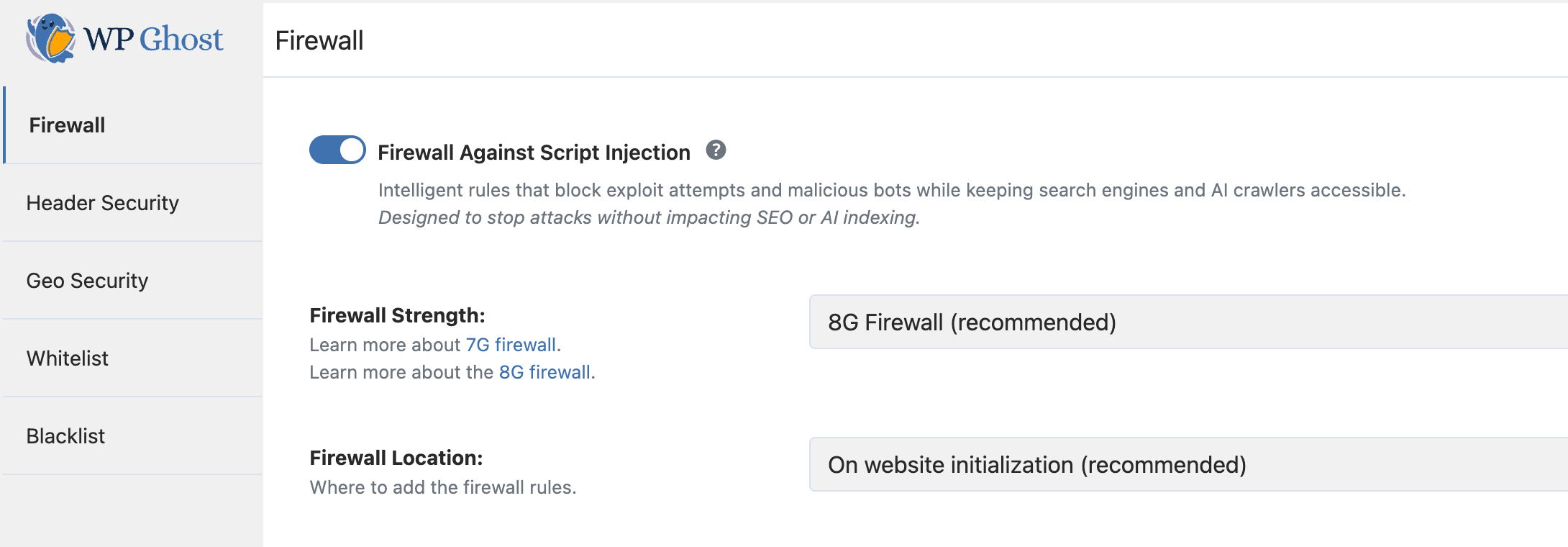
Enable the 8G Firewall in WP Ghost to block SQL injection, script injection, XSS, and directory traversal at the server level before WordPress loads. Free feature, step-by-step guide.
Activate the 7G Firewall in WP Ghost to block SQL injection, script injection, XSS, and malicious bots at the server level before WordPress loads. Free feature, zero performance impact.
Disable WP Ghost path security for administrators, editors, or any WordPress user role using a simple code snippet. Also covers IP whitelisting as a no-code alternative.
Discover the most popular WordPress theme detectors, how they work, which ones to trust for testing, and how WP Ghost makes your site invisible to all of them by securing default paths.
Replace WooCommerce and Elementor class names in HTML, CSS, and JS using WP Ghost Text Mapping so theme detectors can not identify your plugins. Advanced feature with caching guide.
Learn how to protect your WordPress website using WP Ghost path security, 8G Firewall, brute force protection, 2FA, secure hosting, and a complete security checklist to prevent hack attacks.
This tutorial has moved to the new WP Ghost Knowledge Base where each feature is presented in detail.
WP Ghost prevents hack attacks on WordPress by changing default paths, blocking bot traffic with a built-in firewall, and adding brute force protection – stopping threats before they reach your plugins, themes, or login page.
Why WordPress Sites Are Easy Targets
WordPress powers over 43% of all websites on the internet. That popularity makes it the number one target for automated attacks. The problem is not WordPress itself. The problem is the open-source ecosystem around it.
Many plugins and themes are created by developers who are great at building features but not trained in security best practices. A single vulnerable function, an unvalidated input field, or an exposed file path can give a hacker bot everything it needs to inject malicious code into your site. And with over 64,000 tracked vulnerabilities in the WPScan database, new security flaws are discovered every week.
You can not personally audit every plugin you install. You can not guarantee that the next update will not introduce a new vulnerability. What you can do is make sure bots never find those plugins in the first place.
Why Paths Security Matters
Every WordPress site ships with the same predictable structure. Paths like /wp-admin, /wp-login.php, /wp-content/plugins/, and /wp-content/themes/ are identical on millions of websites. Hacker bots do not need to guess. They already know where everything is.
The attack works in two phases. First, the bot scans for default WordPress paths to confirm the target. Second, it runs known exploits against those paths, targeting vulnerable plugins, weak passwords, and exposed endpoints. If the bot can not complete phase one, phase two never happens.
This is why changing and securing your WordPress paths is the most effective form of hack prevention. If bots can not find the doors, they can not break them down.
Default Paths vs. Secured Paths
| WordPress Path | Default (Vulnerable to bots) | Secured with WP Ghost |
|---|---|---|
| Admin dashboard | /wp-admin/ | /your-custom-admin/ |
| Login page | /wp-login.php | /your-custom-login/ |
| Plugins directory | /wp-content/plugins/ | /custom-assets/extensions/ |
| Themes directory | /wp-content/themes/ | /custom-assets/layouts/ |
| Uploads folder | /wp-content/uploads/ | /custom-assets/media/ |
| REST API | /wp-json/ | /custom-api/ |
| Old paths accessible? | Yes (exploitable) | 404 Not Found |
Reactive vs. Proactive Security
Most popular WordPress security plugins focus on detecting threats after they have already reached your site. They scan files for malware, monitor database changes, and alert you when something looks suspicious. That approach is valuable, but it is reactive. It treats the symptoms after the infection.
WP Ghost takes the opposite approach. Instead of waiting for an attack to succeed and then cleaning up the mess, it prevents the attack from happening in the first place. By changing every default WordPress path and filtering malicious requests at the server edge, WP Ghost eliminates the attack surface before bots even confirm your site runs WordPress.
Think of it this way: reactive plugins are the alarm system that alerts you after someone breaks in. WP Ghost is the architecture that makes the doors and windows invisible so nobody attempts to break in at all.
How WP Ghost Prevents Hack Attacks
WP Ghost provides multiple layers of hack prevention that work together to protect your site:
Path Security
WP Ghost changes and secures every common WordPress path, including wp-admin, wp-login.php, wp-includes, wp-content, plugins, themes, uploads, REST API, author paths, comments path, admin-ajax.php, and more. It also hides common files like wp-config.php, readme.html, license.txt, and debug.log. No files are physically moved or renamed. WP Ghost uses server rewrite rules and WordPress hooks, so deactivating the plugin restores all defaults instantly. For the complete path security guide, see Customize Paths with WP Ghost.
8G Firewall
The built-in 8G Firewall operates at the server edge, filtering out SQL injection, script injection, cross-site scripting (XSS), file inclusion exploits, and directory traversal attacks before they reach your WordPress core or database. Because it works through lightweight server rules, malicious requests are blocked before PHP even loads. This means zero performance impact on your legitimate visitors. Learn more at Firewall Security.
Brute Force Protection
WP Ghost protects your login page, registration form, lost password form, and comment forms with Math reCAPTCHA, Google reCAPTCHA V2, and Google reCAPTCHA V3. You can set custom attempt limits, timeout durations, and custom messages. Combined with a changed login path, bots can not even find the login page, let alone brute-force it. See the full setup at Brute Force Protection.
Two-Factor Authentication
Even if an attacker somehow obtains a password, 2FA stops them at the door. WP Ghost supports 2FA by code (Google Authenticator), 2FA by email, and 2FA by passkey, including Face ID, Touch ID, Windows Hello, and hardware security keys. All three methods are included in the free version. Set it up at Two-Factor Authentication.
Security Headers
WP Ghost adds browser-level protection through security headers like Strict-Transport-Security, Content-Security-Policy, X-Frame-Options, X-Content-Type-Options, and X-XSS-Protection. These headers prevent clickjacking, content sniffing, and cross-site scripting at the browser level. Configure them at Header Security.

Works Together with Other Security Plugins
WP Ghost is designed to complement, not replace, other security tools. It works alongside Wordfence, Solid Security, Shield Security, Sucuri, and many others. While those plugins focus on malware scanning and file integrity monitoring (reactive security), WP Ghost focuses on preventing attacks from reaching your site (proactive security). Use them together for full defense in depth.
You do not need to deactivate other security plugins when you install WP Ghost. For the full list of tested plugins, see the Plugin Compatibility List.
Getting Started
WP Ghost is free to install from the WordPress directory and includes 115+ security features out of the box, including path security, the 8G Firewall, brute force protection, 2FA with passkeys, security headers, and temporary logins. Premium adds 35+ features for a total of 150+ including the Security Threats Log, Country Blocking, IP Block Automation, and priority support.
For the recommended setup, follow these guides:
1. Set Up WP Ghost in Safe Mode in 3 Minutes
2. WP Ghost Settings Best Practice
3. Verify Your Site Is Protected
Frequently Asked Questions
Can WP Ghost prevent all hack attacks on WordPress?
WP Ghost eliminates the attack surface that bots use to find and exploit vulnerabilities. When properly configured, it blocks up to 99% of automated bot attacks. However, no single plugin can guarantee 100% protection. WP Ghost should be part of a layered security strategy that includes regular backups, strong passwords, keeping plugins updated, and secure hosting.
Is WP Ghost enough or do I need Wordfence too?
For most WordPress sites, WP Ghost provides a comprehensive hack prevention foundation on its own. If you want additional malware scanning and file integrity monitoring, you can run Wordfence alongside WP Ghost. They handle different security layers and complement each other well. See the WP Ghost and Wordfence compatibility guide for the recommended configuration.
Does WP Ghost slow down my website?
No. WP Ghost is built for zero-bloat performance. The firewall operates at the server edge using lightweight rules, and path security works through rewrite rules rather than heavy database scans. Most users see no measurable impact on page load time. In fact, by blocking bot traffic before it reaches WordPress, WP Ghost can actually reduce server load.
Does WP Ghost modify WordPress core files?
No. WP Ghost uses server rewrite rules (.htaccess on Apache, config files on Nginx) and WordPress hooks. No core files are moved, renamed, or modified. Deactivating the plugin restores all default paths instantly.
Does this work with WooCommerce?
Yes. WP Ghost is fully compatible with WooCommerce. Cart, checkout, product pages, customer accounts, and AJAX-powered features all work normally with secured paths.