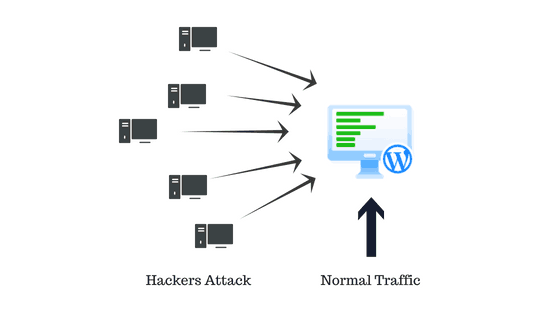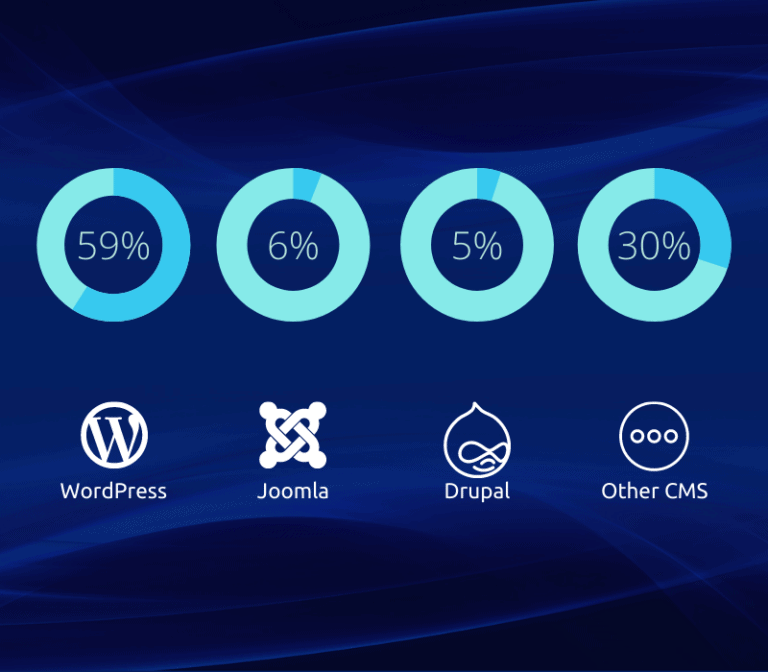

Which Websites are Targeted by Hackers?
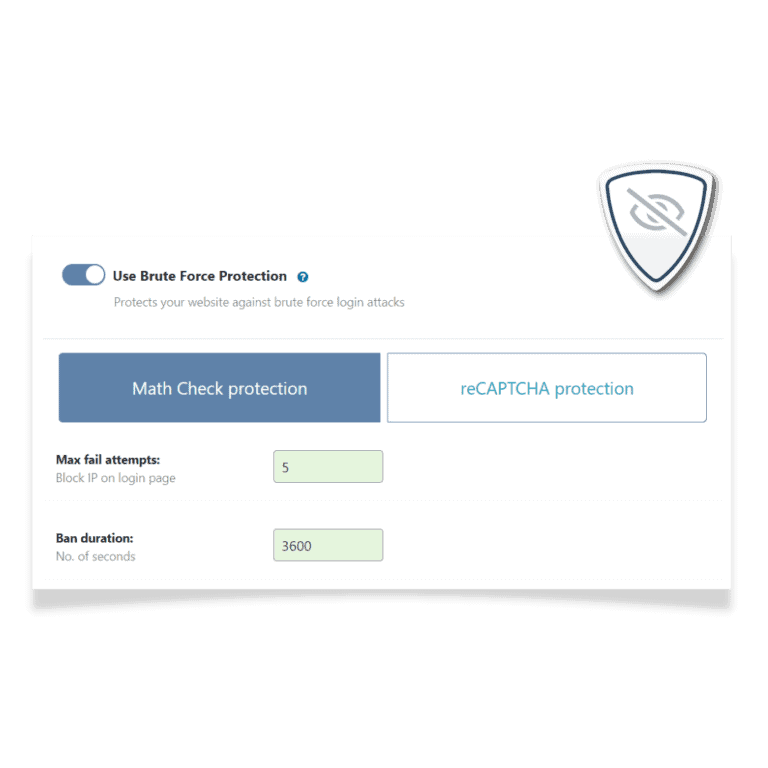
Brute force attacks are common against popular CMS platforms (e.g., WordPress, Joomla, etc.) and against common services, such as FTP and SSH. Statistics show that WordPress has been the most affected CMS in recent years.
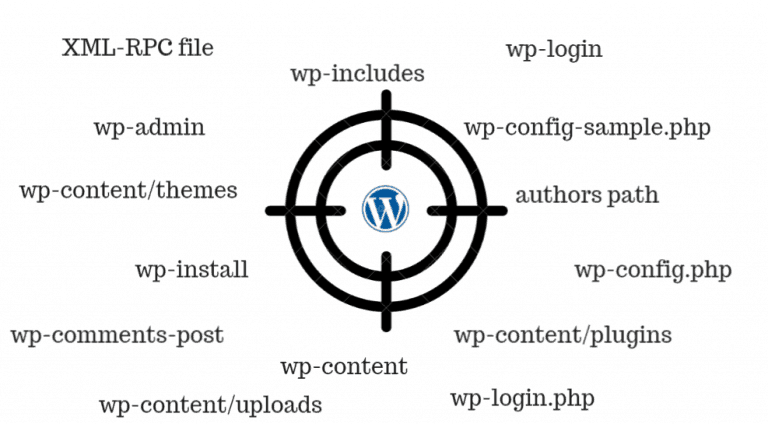
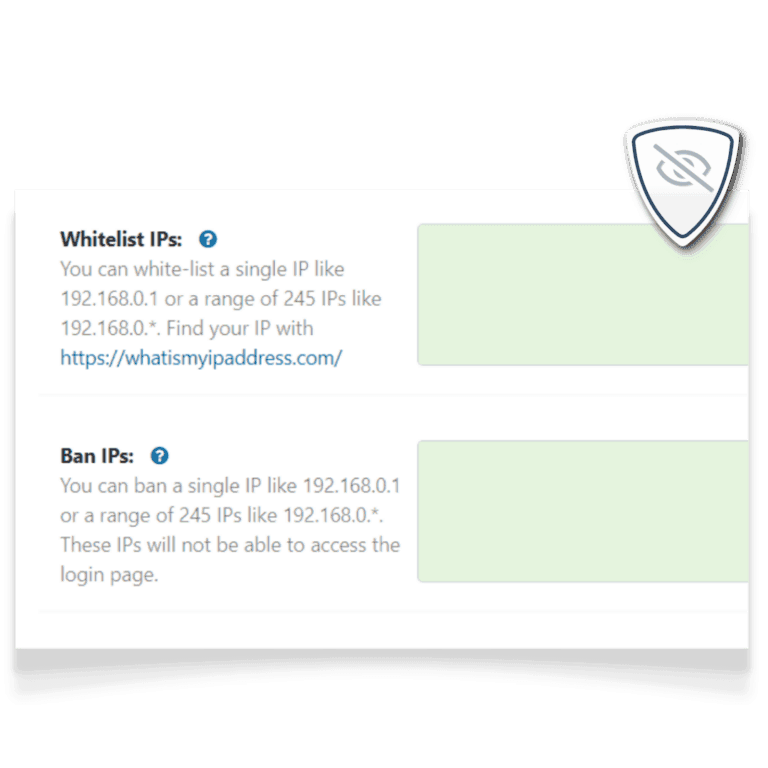
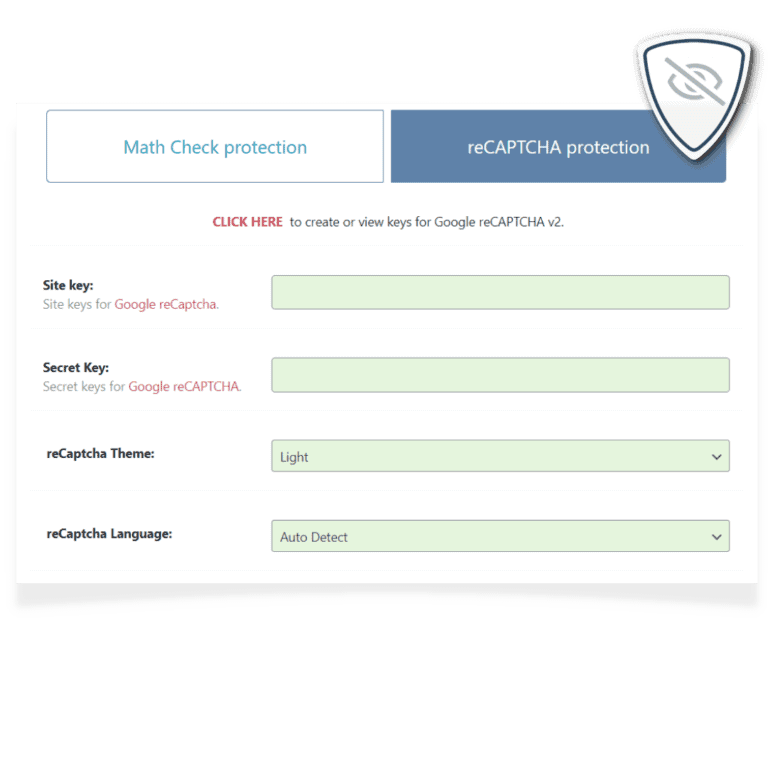
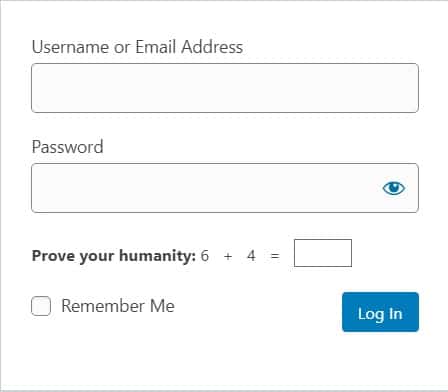
Most brute force attacks work by targeting a website, typically the login page and the xmlrpc.php file.
Usually, every common ID (e.g., “admin”) has a password. All hackers need to do is guess the password based on words in a dictionary.