How to Disable XML-RPC Access in WordPress with WP Ghost
This tutorial has moved to the new WP Ghost Knowledge Base where each feature is presented in detail.
Disable WordPress XML-RPC access with WP Ghost (formerly Hide My WP Ghost) to block brute force amplification attacks, DDoS pingback abuse, and CMS fingerprinting through xmlrpc.php. The system.multicall method lets attackers send up to 1,999 password guesses in a single HTTP request. Disable it, and that entire attack vector is eliminated.
XML-RPC is WordPress’s legacy remote communication protocol. It predates the REST API and is rarely needed by modern sites. The REST API handles everything XML-RPC used to do: remote publishing, mobile apps, third-party integrations, and admin automation. But XML-RPC remains enabled by default on every WordPress installation, and it is one of the most abused endpoints on the internet.
The most dangerous XML-RPC method is system.multicall. It bundles multiple calls into a single HTTP request. Attackers exploit it to send hundreds of password guesses in one request, up to 1,999 per call in known exploit tools. Standard login protections (rate limiting, CAPTCHA, failed login tracking) see it as one request, not 2,000. That is why it is called brute force amplification.
Why You Need to Disable XML-RPC
| With XML-RPC enabled (default) | With XML-RPC disabled (WP Ghost) |
|---|---|
| system.multicall sends 1,999 password guesses per request | xmlrpc.php returns 404, amplification impossible |
| Pingback abuse enables DDoS amplification | Pingback method returns nothing |
| xmlrpc.php confirms WordPress to scanners | CMS fingerprint eliminated |
| Each auth attempt consumes server CPU and database | Requests blocked before reaching WordPress |
How to Disable XML-RPC with WP Ghost
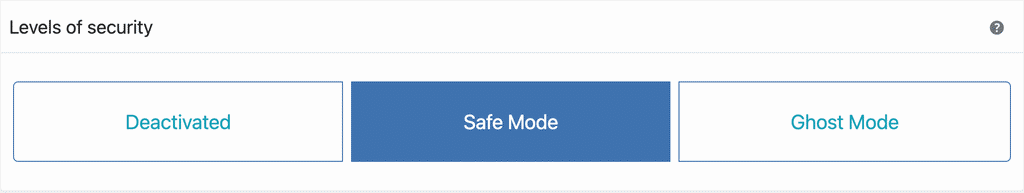
Activate Safe Mode or Ghost Mode
Go to WP Ghost > Change Paths > Level of Security. Select Safe Mode or Ghost Mode and click Save.
Disable XML-RPC Access
Go to WP Ghost > Change Paths > API Security. Switch on Disable XML-RPC Access. Click Save.
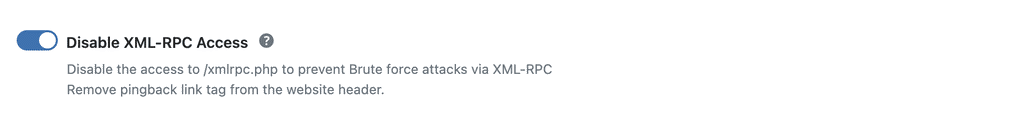
Once disabled, the xmlrpc.php file no longer responds to requests. Anyone trying to access it gets a 404 error instead of the default “XML-RPC server accepts POST requests only” message.
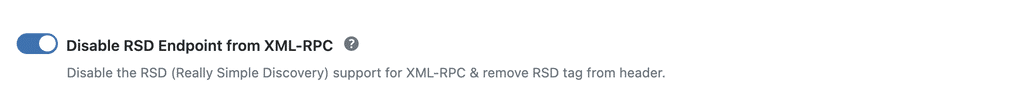
Disable the RSD Endpoint
RSD (Really Simple Discovery) is a protocol that advertises your site’s XML-RPC endpoint in the HTML header. Theme detectors and scanners use this header to confirm WordPress and locate the XML-RPC file. Disabling it removes the RSD META link and the rsd_link header from your page source.
Go to WP Ghost > Change Paths > API Security. Switch on Disable RSD Endpoint from XML-RPC. Click Save.
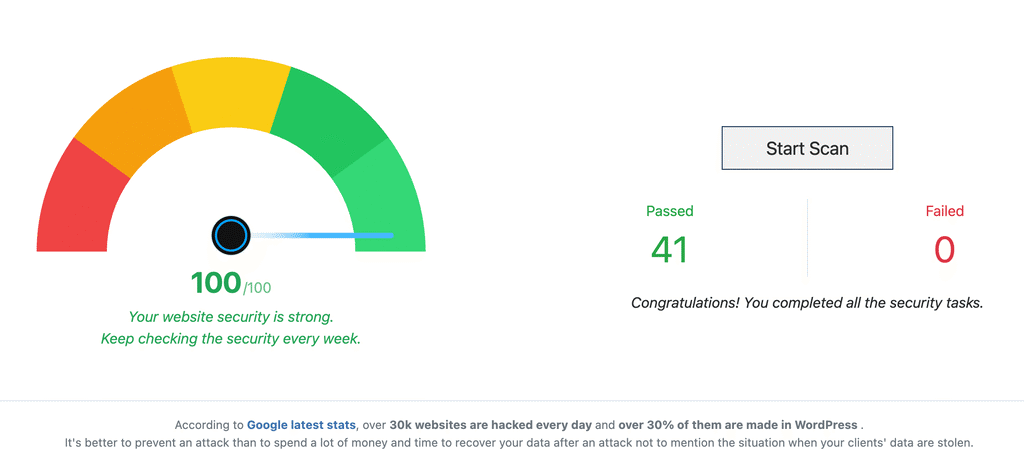
Verify with a Security Check
Go to WP Ghost > Security Check. Click Start Scan. The scan confirms XML-RPC is disabled and the RSD endpoint is removed.
For a quick manual test, visit yourdomain.com/xmlrpc.php in your browser. If you see a 404 error instead of the “XML-RPC server accepts POST requests only” message, the protection is active.
JetPack Compatibility
Jetpack uses XML-RPC for some of its communication with WordPress.com servers. If you use Jetpack and need to keep XML-RPC accessible to its servers while blocking everyone else, add Jetpack’s IP ranges to your .htaccess file instead of using the WP Ghost toggle.
Add the following at the beginning of your .htaccess file:
<Files xmlrpc.php> Order deny,allow Deny from all Allow from 127.0.0.1 Allow from *.wordpress.com Allow from 192.0.64.0/18 Allow from 185.64.140.0/22 Allow from 2a04:fa80::/29 Allow from 76.74.255.0/22 Allow from 192.0.65.0/22 Allow from 192.0.80.0/22 Allow from 192.0.96.0/22 Allow from 192.0.123.0/22 Satisfy All ErrorDocument 404 / </Files>
This blocks all access to xmlrpc.php except from Jetpack’s servers and localhost. For the latest Jetpack IP ranges, visit the Jetpack IP documentation. If you do not use Jetpack, just disable XML-RPC entirely through WP Ghost.
Frequently Asked Questions
What is system.multicall and why is it dangerous?
system.multicall is an XML-RPC method that bundles multiple calls into a single HTTP request. Attackers exploit it to send hundreds of password guesses in one request, up to 1,999 per call in known exploit tools. Standard login protections see it as one request, not 2,000. That is why it is called brute force amplification and it is the primary reason XML-RPC is dangerous.
Do I need XML-RPC for anything?
Almost certainly not. The REST API has replaced XML-RPC for every modern use case: remote publishing, mobile apps, third-party integrations, and admin automation. The only notable exception is Jetpack, which uses XML-RPC for some features. If you use Jetpack, see the compatibility section above.
What is the difference between XML-RPC and the REST API?
Both allow remote communication with WordPress, but they are different systems. XML-RPC is the older protocol that sends credentials in plaintext with every request. The REST API is the modern approach that uses JSON, supports authentication tokens, and has proper rate limiting support. WordPress itself uses the REST API for the block editor and all admin functions.
Will disabling XML-RPC break my site?
No. The REST API handles everything XML-RPC used to do. The block editor, admin dashboard, plugin updates, and all admin functions work through the REST API, not XML-RPC. Visitors see no change at all.
Does WP Ghost modify WordPress core files?
No. WP Ghost blocks XML-RPC access through WordPress filters and rewrite rules. The xmlrpc.php file stays on the server but no longer responds to requests. Deactivating WP Ghost restores default behavior instantly.
Related Tutorials
Change REST API Path – secure the modern API endpoint alongside XML-RPC.
Customize All WordPress Paths – change every WordPress path including API endpoints.
Brute Force Attack Protection – add reCAPTCHA and login attempt limits.
Firewall and Geo Security – block malicious traffic with the 8G Firewall.
Website Security Check – verify XML-RPC is disabled and all settings are applied.